Hackers are being caught exploiting the Zero-Day bug more than ever
Previously unspecified”no day“Software vulnerabilities are a mysterious and fascinating concept. But they are even more noticeable as hackers are found to be actively exploiting new software bugs in the wild before anyone else knows about them. As researchers expand their focus to discover and study more of this exploit, they’ll see it more often. Two reports this week from threat intelligence firm Mandiant and Google’s bug-hunting team, Project Zero, aim to provide insight into the question of exactly how much zero-day exploits have evolved in the past year. Lately year.
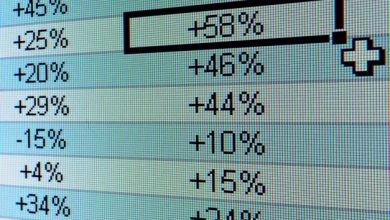
Mandiant and Project Zero both have a different range for the types of zero-days they track. For example, Project Zero does not currently focus on analyzing vulnerabilities in wild-exploited internet-connected devices. As a result, the absolute numbers in the two reports cannot be directly compared, but both pools have tracked a record high number of zero days of mining in 2021. Mandiant tracks 80 last year versus 30 in 2020 and Project Zero tracks 58 in 2021 compared to 25 years ago. The key question for both groups, however, is how to contextualize their findings, as no one can see the full scale of this covert operation.
Maddie Stone, a security researcher at Project Zero, said: “We started seeing the spike in early 2021, and a lot of the questions I got throughout that year were, ‘What the hell is going on so ?!’. “My first reaction was, ‘Oh my gosh, there are so many.’ But when I take a step back and look at the context of previous years, to see such a big leap forward, that growth is actually more likely due to increased detection, transparency and understanding. widely known about zero-day. ”
Before a software vulnerability is publicly disclosed, it is called a “no day, ” Because there is no day when a software maker can develop and release a patch, and there is no date for defenders to start tracking vulnerabilities. In turn, the hacking tools that attackers use to take advantage of such vulnerabilities are known as zero-day exploits. Once a bug becomes publicly known, a fix may not be released immediately (or ever), but attackers find that their activity can be discovered or that the vulnerability can be discovered. Plug in at any time. Therefore, zero-day is very popular and big business for both criminals and especially government-backed hackers who want to conduct both mass campaigns and suitable, personal targeting.
Zero-day vulnerabilities and exploits are often considered uncommon and proven attack tools, but governments have repeatedly demonstrated them. zero-day stockpileand increased detectability revealed how often attackers deployed them. Over the past three years, tech giants like Microsoft, Google, and Apple have begun to normalize the note when they disclose and fix a vulnerability that was exploited prior to the release of a patch.
While detection and awareness efforts have increased, James Sadowski, a researcher at Mandiant, emphasizes that he sees evidence of changing landscapes.